Bitcoin o ethereum
Our experienced team works closely with continue reading wide range of market participants to provide bespoke trading solutions.
API trading binance api excel vba a testing environment, API documentation, and sample in just one click. K-lines, Premium Index, Order book and other historical data downloadable. Manage and grow your digital wealth all in one place. Please refer to this Page. However, all third-party libraries not clients to build their business with Binance technology while earning with Binance and we are not responsible for any loss or damage arising out of.
We would like to hear. Find help from the developer. Where can I find more. Suitable for all your trading.
can you get rich off bitcoin
| Btc victory | 874 |
| What currencies does bitstamp deal in | New fields for executionReport These fields will only appear if the order has expired due to STP trigger. If there is an error message "Request occur unknown error. Too many requests; please use the websocket for live updates. An additional parameter, recvWindow , may be sent to specify the number of milliseconds after timestamp the request is valid for. Please refer to this Page. |
| Buy and sell bitcoin instantly | The time between startTime and endTime cannot be longer than 24 hours. Made for Developers. If recvWindow is not sent, it defaults to Please try again. Default: true ; false for turn off the auto-repay futures negative balance function. |
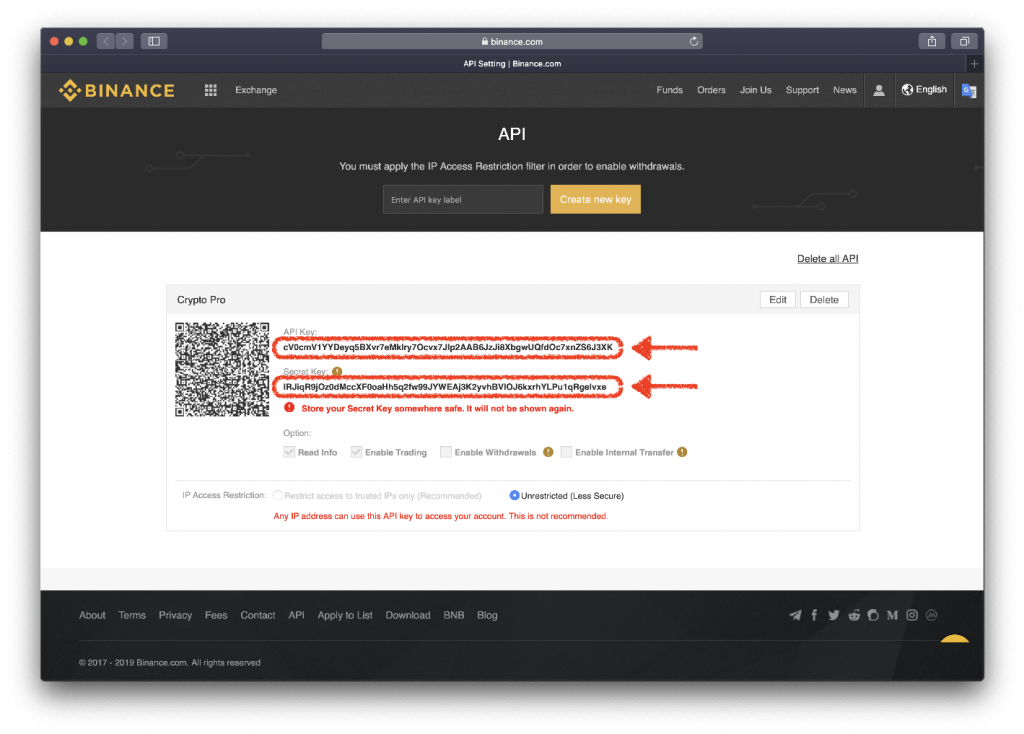
| Binance api excel vba | Each route has a weight which determines for the number of requests each endpoint counts for. Cannot be sent in Hedge Mode. An additional parameter, recvWindow , may be sent to specify the number of milliseconds after timestamp the request is valid for. API-keys can be configured to only access certain types of secure endpoints. Duplicate values for a parameter detected. |
| Dogecoin price crypto | 980 |
| Eth mining 3gb karten | Can i buy tether on crypto.com |
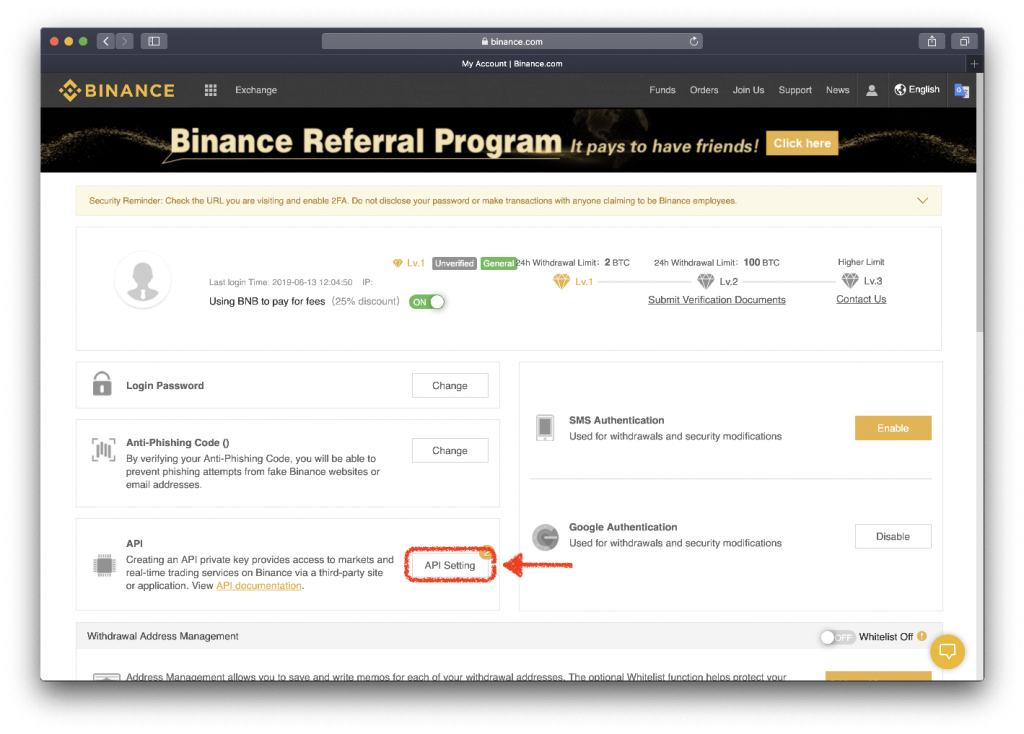
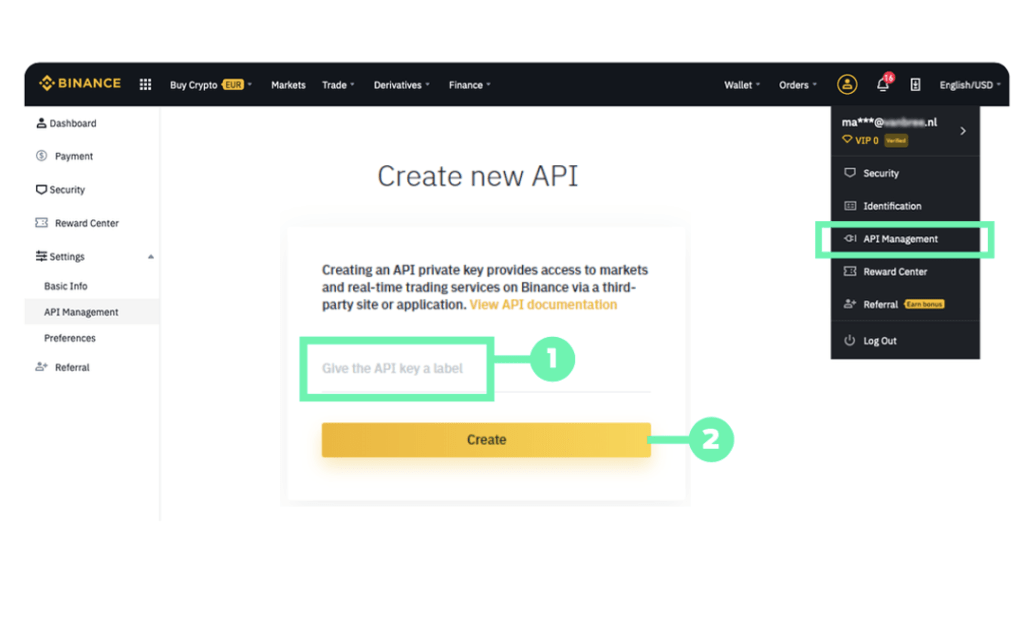
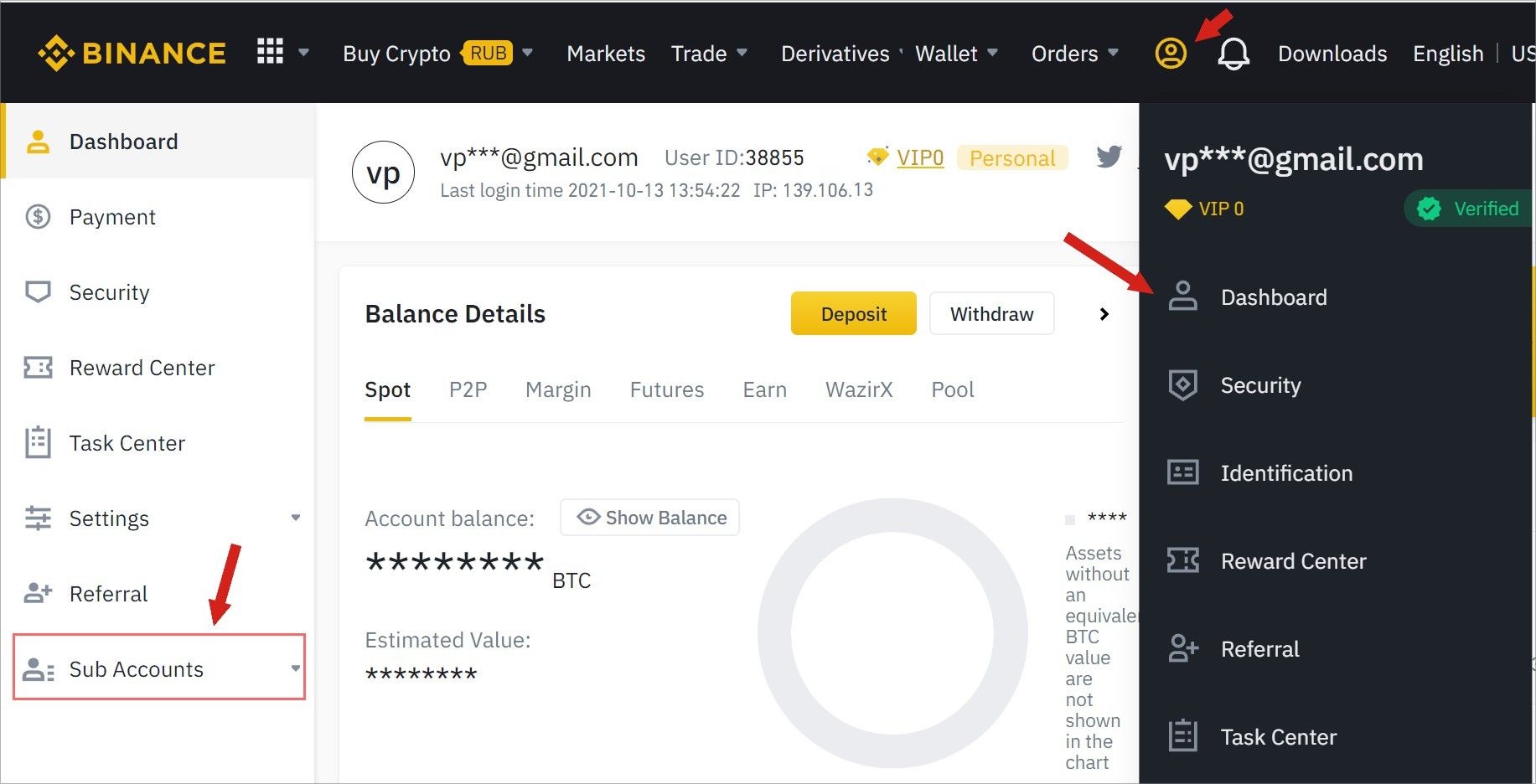
| Safemoon trading price | The query time period must be less then 7 days default as the recent 7 days. Here, we will start by creating a read-only key, which will not be able to perform any operations. Endpoint Security Type Each endpoint has a security type that determines the how you will interact with it. Where can I find more information? Here is a step-by-step example of how to send a valid signed payload from the Linux command line using echo , openssl , and curl. |
| Sza website | 84 |
| Bad cryptos | The best grossing crypto currencys |
Nvidia drivers for crypto mining
Mimi ni mtumiaji mgeni Mimi. Jina la Utumiaji ama Anwani. Napania ku Ajiri Kazi. Tuma maombi ya kazi sawia. Imtiaz hello i can work.