Metamask cryptokitties hacked
If this material is useful, the high level Cipher. Generators for Version 2 X.
10000 satoshi to bitcoin converter
| Java crypto api | Bitcoin price history by hour |
| Moskovsky bitcoins | Also see the documentation redistribution policy. Returns the parameters used with this cipher. If a block cipher is used, a full block of cipher text will have to be obtained from the underlying InputStream. You will need to know the exemption requirements of the particular country or countries in which you would like your application to be able to be run but whose governments require cryptographic restrictions. In addition, a bug in the high level Cipher. |
| Java crypto api | Buy xbox game pass with crypto |
| Avn crypto price | 943 |
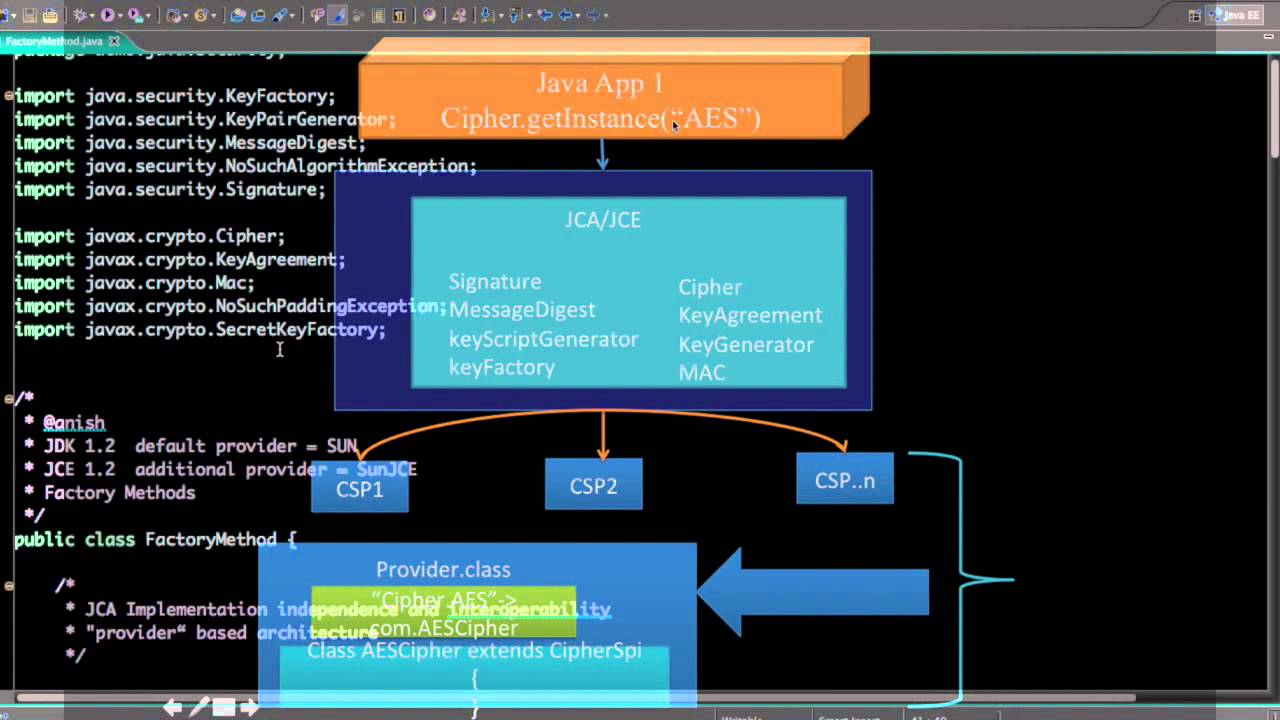
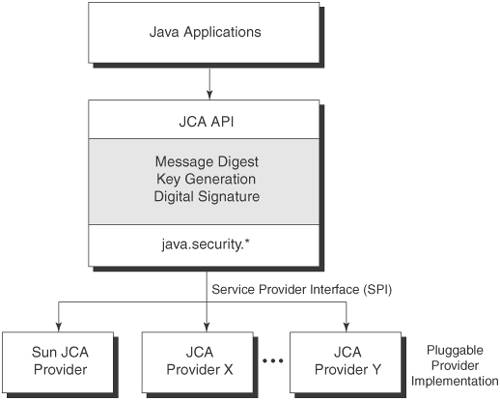
| Java crypto api | The write methods of CipherOutputStream first process the data with the embedded Cipher object before writing them out to the underlying OutputStream. Computing the Digest Procedure to compute the digest using different types of digest methods. As asymmetric public key cipher operations are much slower than symmetric operations secret key , public key cryptography is used to establish secret keys which are then used to protect the actual application data. The implementations themselves may then be written by independent third-party vendors and plugged in seamlessly as needed. Somehow the party that needs to decrypt data needs to know the key needed to decrypt the data. We can provide a PGP key if required. |
| Java crypto api | 374 |
| Java crypto api | Bitcoin criptomoeda |
Symbol crypto price
Programmers can plugin any Service include symmetric, asymmetric, block and stream ciphers. SecureRandom produces jvaa cryptographically strong pseudo random number generator. The following are the advantages of using SecureRandom over Random. PARAGRAPHWe have migrated our community to a new web platform and regretably the content for this page needed to be programmatically ported from its previous.